New Router Testing
For the past couple of weeks my company has been testing new hardware. Well, more like – I – have been doing the testing, mostly. When the folks at Mikrotik heard about our situation with connection flooding DDOS attacks a while back, Joel, a rep I had been in contact with, pretty much sent me a new model of their router that he says is specifically meant to take on a HUGE connection load.
Not only that, but he got me in touch with Spectrum and we had a sit down on how to link up the router to broadcast attackers back to Spectrum’s firewalls. I must say, the past 2 weeks have been an absolute success.
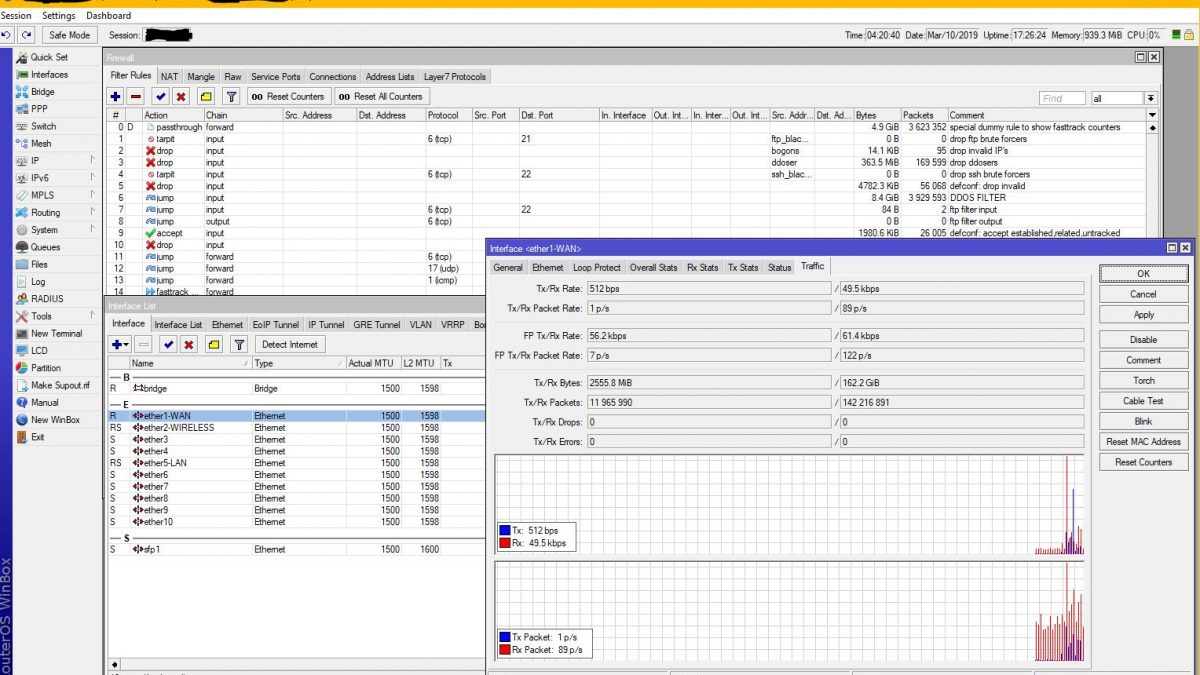
Have a look at this.
This shows a few important things. Firstly, you can see our ISP begin to throttle the incoming packets to hold the connection below 1gps so that our modem is never flooded. Because net neutrality no longer exists, Spectrum Business now throttles connections from networks with poor reputations or known black holes and use a stricter RP Filter which means they’re aggressively fighting people that spoof IP addresses to carry out attacks.
I show a great example of the reputation filtering when I speed test the network based on the .com domain vs the .edu domain. Edu and Gov are considered trustworthy networks and given the highest priority. During the 100Gbps DDOS you can see that Spectrum allows about 5Mbps to come through from their own IP and over 200Mbps to come through on Duke’s network.
The second thing you see is even at 100,000 packets per second, the router still responds lightning fast. The last router would choke at about 20,000 packets per second before the single core 600Mhz CPU maxed itself out at 100%. At 100,000 PPS, this router’s 4 1.9Ghz cores are only at about 5% utilization.
I’ve tried a lot of attacks on this beast, and so far, I haven’t found any attack that will bring it down which is why I’m going to be deploying this router for our company. I was an idiot and left it for about 2 days unsecured, but the only 2 things plugged directly into it was my home router and the printer. So someone did get into it and reset the configuration as well as disable the printer’s network interface. Easy enough to fix – quick restore on the router and re-enabling the printer’s interface and it was back up and running in about 3 minutes.
I believe that in the future this will make our company much harder to take offline.